Apps include several serious security flaws that hackers can simply take advantage of. There will be terrible repercussions if security is handled poorly. Attackers take advantage of a variety of vulnerabilities, including lax server-side security, unsecured data interchange, unsecure data storage, weak third-party components, etc. Recently, there has been a steady growth in the number of vulnerabilities.
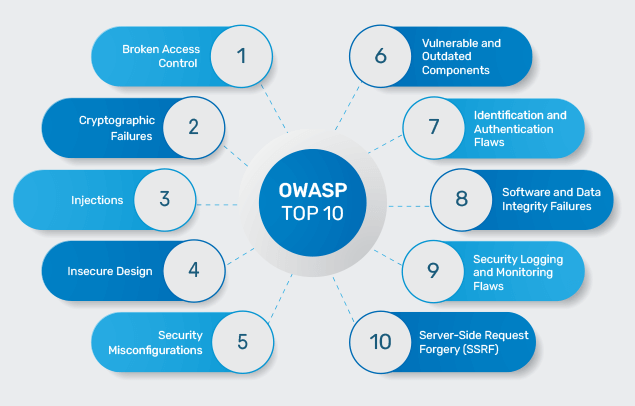
Companies should improve their security measures to stop the exploitation of both recent and historical vulnerabilities. The Open Web Application Security Project (OWASP) is a non-profit group with the mission of enhancing software security. To help businesses address security issues in the upcoming years, this article will take you through the updated OWASP Top 10 Vulnerabilities for 2022 list.
Three new categories are included in the updated list, along with four categories that have had their names and scopes changed. The updated list was developed by OWASP with an emphasis on CWEs’ underlying causes. Eight of the list’s ten categories were developed using the data that was gathered. The Top 10 community survey is used to create the remaining two categories. Let’s examine each vulnerability in turn, along with the remedies that can be used to resolve each.
1. BROKEN ACCESS CONTROL- Attackers may access user accounts due to a flaw in the access control system. To access sensitive files and unlawful data, the attacker logs into the system as a user or administrator and alters user privilege settings with the aid of broken access control weaknesses. Several approaches to deal with this vulnerability include detecting cross-site forgeries, implementing interactive application security testing (IAST) solutions, penetration testing to complement IAST activities, and removing no longer active accounts.
2. CRYPTOGRAPHIC FAILURES- When data is compromised in any way while being transmitted or stored, this is known as a cryptographic failure. Cryptographic mistakes frequently lead to credit card fraud or identity theft. Data transmission in plain text, usage of antiquated techniques, insecure key rotation and management procedures cause cryptographic failures. Turning off autocomplete and catching on forms collecting data, reducing the data surface area size, using up-to-date encryption techniques, and saving passwords using hashing procedures are remedies to this.
3. INJECTION- Assaulting the interpreter with malicious data by using SQL, OS, NoSQL, or LDAP injection is referred to as an injection vulnerability. Attacks are known as “injections” force applications to produce commands that weren’t meant for them to or act in ways that weren’t in their original design by tricking the interpreter into doing so. Its prevention techniques are including SAST and IAST tools in the CI/CD workflow, preventing needless command execution brought on by vulnerability to attacks, separating commands from data, etc.
4. INSECURE DESIGN- Any errors resulting from subpar control design are referred to be insecure design. Threat modelling, secure design patterns, and reference architectures fall under this area. Alternatives to insecure design are using a secure development lifecycle, establishing a collection of readily available secure design patterns, implementing threat modelling, plausibility checks into every level of the application, and limiting user and service resource use
5. SECURITY MISCONFIGURATION- All vulnerabilities have security misconfiguration as their most prevalent flaw. Accepting insecure default settings, imperfect configurations, verbose error messages containing confidential information, and incorrectly configured HTTP readers are to blame for security misconfiguration. Remedies to these issues include utilizing templates compliant with the organization’s security policies, using segmented application architectures, you can lower risk, and keeping an eye out for security setup errors by continuously monitoring cloud resources, servers, and applications.
6. VULNERABLE AND OUTDATED COMPONENTS- There is a serious risk to the application’s security from open-source components’ potential flaws. The main factor in a data breach is frequently vulnerable components. Applying configuration to parts that are included in corporate frameworks, and automating patch management operations will lower operational risk associated with patching, scanning against a vulnerability database that has been enhanced with threat intelligence data are solutions to this.
7. IDENTIFICATION AND AUTHENTICATION FAILURES- When application activities relating to session management or user authentication are carried out incorrectly, attackers can compromise passwords, session tokens, or security keys. In turn, user identities are taken. Failures in identification and authentication could jeopardise the safety of other assets on the same network.
Using multi-factor authentication, not allowing admin users to log in using the default credentials, assessing all failed login attempts, deploying a secure session manager, and avoiding including session IDs in URLs are some solutions to this.
8. SOFTWARES AND DATA INTEGRITY FAILURES- The dangers of this vulnerability include malicious programming and unapproved access. Applications that use libraries, plugins, or modules from unreliable sources are prone to integrity issues. Updates are applied without the necessary integrity checks due to the auto-update capability. Solutions are to make sure the application hasn’t been tampered with, use digital signatures, guarantee the application of a review process for changes to configuration and code, check to see if the dependencies and libraries are utilising reliable repositories, verify that the segregation, setup, and access control in your CI/CD pipeline is sufficient, never allow unencrypted data to reach unreliable clients.
9. SECURITY LOGGING AND MONITORING FAILURES- Failures in logging and monitoring expose an application to threats. A vulnerable application will be created if login attempts and failures are not registered and monitored. It can be addressed by carrying out penetration testing to review test logs and identify any issues, preventing tampering, ensuring high-value transactions have an audit trail, generating logs in a format that log management solutions can readily consume, putting in place an alerting and monitoring system to spot suspicious activity, and properly encoding all log data.
10. SERVER SIDE REQUEST FORGERY- A common cause of this is when a programme retrieves a remote resource without first checking the user-supplied URL. The use of server-side request forgeries has increased recently due to complex architectures and rising cloud service usage. Its mitigation techniques include applying firewall rules that “deny by default”, verifying URL correctness and sanitising client-supplied input data, etc.
You can avoid potential losses in money and reputation by adhering to this list. The addition of additional categories in the updated list emphasises the significance of security from the very beginning of the design. For strong defence for Android, iOS, and hybrid apps, Appsealing specialises in mobile app security solutions. Together with offering real-time runtime protection, we make sure third-party products are simple to use. Get in touch with us right away to take advantage of effective code protection that does not affect app performance.